How to configure inSync and SAML?
- Only a Druva Cloud administrator can set up Single Sign-on.
- Configure Single Sign-on based on the applicable scenarios:
- New inSync customers (on-boarded after July 14, 2018) must configure Single Sign-on using the Druva Cloud Platform Console. For more information, see Set up Single sign-on.
- Existing inSync customers who have not configured Single Sign-on until July 14th, 2018, must configure Single Sign-on using the Druva Cloud Platform Console. For more information, see Set up Single sign-on.
Overview
This article describes how to configure SAML Single Sign on with inSync.What is covered:
What is SAML?
Security Assertion Markup Language (SAML 2.0) is a version of the SAML OASIS standard for exchanging authentication and authorization data between security domains, i.e. between an identity provider (a producer of assertions) and a service provider (a consumer of assertions). SAML enables web-based authentication and authorization scenarios including single sign-on (SSO).
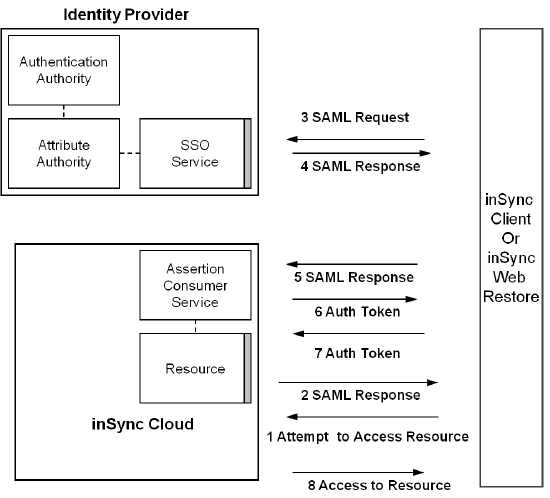
The following diagram represents a typical SAML request and response cycle for inSync.
SAML authentication for Single Sign on
The single sign-on option authenticates the user and facilitates him to activate a device in inSync, or gain access to all his devices connected to his account when using inSync Web restore.
How inSync uses SAML:
1. While logging in to inSync, user enters the inSync Cloud URL in the Server field.
2. User enters the e-mail address and leaves the password field blank.
3. Now the inSync client redirects to the configured ID Provider’s authentication page, via a SAML Request.
4. Here the user types Username and Password.
5. The issuing authority (IdP) returns a SAML assertion to inSync client.
6. The inSync client automatically submits the assertion to Druva server, which validates the SAML Response and then logs the user in.
For more information on installing and configuring the Active Directory Federation Services for Druva SAML integration contact Druva support.
Configure inSync for SAML
inSync can be configured to talk to SAML 2.0 compliant ID providers to offload authentication for device activation as well as Web-restore.
- On inSync Management Console, click
 >Settings.
>Settings. - Click the Single-Sign on tab and then click Edit. The Single Sign-On Settings window appear.
- Enter following Single Sign-On configuration details about the issuing authority on the window: .
- ID Provider Login URL: The URL where your organization sends a SAML request to start the login sequence. (This field is mandatory.)
- ID Provider Certificate: The authentication certificate issued by your identity provider. (This field is mandatory.)
- AuthnRequests Signed: Enables signed SAML Authentication Requests (Optional). In a Server Provider (SP) initiated Single Sign-On (SSO), the authentication request (AuthnRequest) can specify to which Assertion Consumer Service (ACS) the Security Assertion Markup Language (SAML) response has to be sent.
- Want Assertions Encrypted: Enables encryption for SAML assertions (Optional). Encryption is disabled by default. Use this option to first sign in and then encrypt a SAML request using the public key of the identity provider and then transmit over SSL.
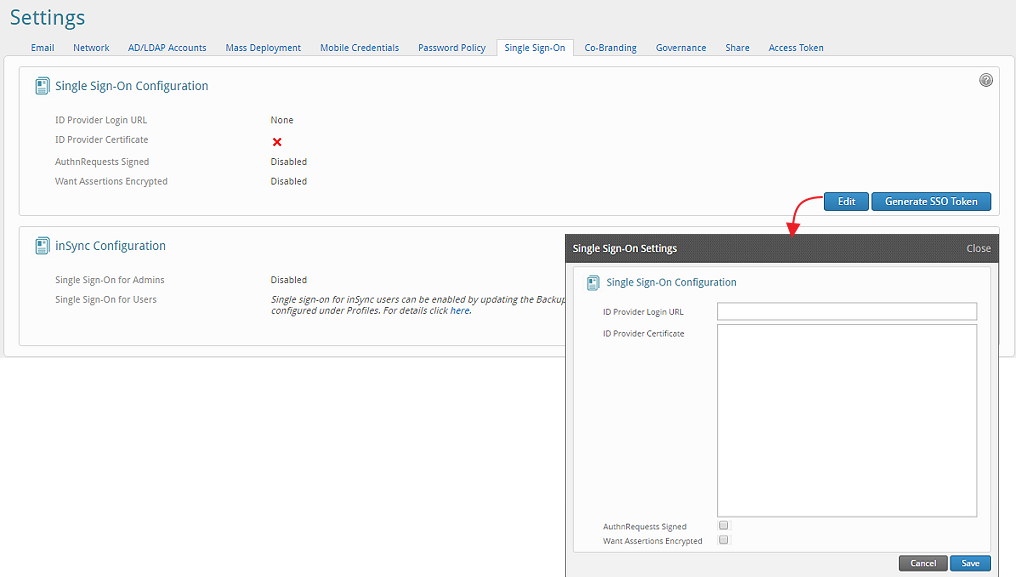
You will also need to generate a SSO token that is used on the IdP site.
Creating a new token
inSync Cloud single sign-on requires a customer-specific token that is returned to the inSync Cloud service along with each authenticated user response. This is needed to implement Druva’s secure password mechanism. This token isn’t saved on the server in any way. This token is to be handled as you would the key of a PKI key pair and needs to be pasted in the Id Provider configuration to complete the Single Sign-on setup for inSync Cloud.
Configuring a SAML 2.0 IdP for use with inSync Cloud
If you already have a SAML 2.0 compliant IdP configured this is how you can set it up correctly to be able to talk to the inSync Cloud service provider.
These generic instructions should map to all major IdP services fairly easily. Please contact inSync Support for questions or queries regarding any specific SAML Id Provider.
Enter the following details while configuring the IdP:
Service Name: Use whatever you’d prefer to use to refer to inSync Cloud. 2. Issuer: ‘druva-cloud’
AssertionConsumerService endpoint: https://cloud.druva.com/wrsaml/consume
NameIDFormat: 'urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress'
SingleLogoutService: https://cloud.druva.com/webrestore/dologout
‘insync_auth_token’: This is a custom attribute that needs to be present in all SAML assertion response if authentication succeeds. The value of this attribute comes from the SAML configuration page on the inSync Cloud Settings section. Please see Create New Token above.

