How to configure inSync GovCloud SSO for inSync users using Azure AD as IdP
This article applies to:
- Product edition: inSync GovCloud
Overview
This article describes the steps to configure SSO for inSync users to access inSync GovCloud using Azure AD as IdP.
The SSO is configured in the following order:
Configure a custom app for Druva inSync on Azure portal
- Log on to the Azure portal (URL: portal.azure.com)
- Log on using Azure Administrator account.
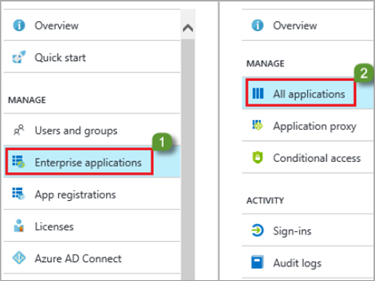
- Navigate to Azure Active Directory > Enterprise Applications.
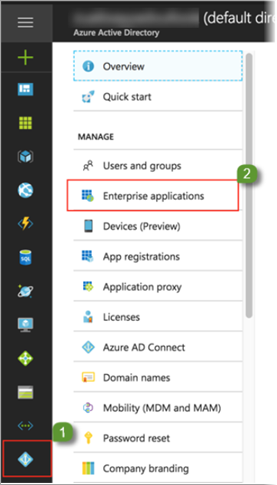
- On the Enterprise applications page, click New application.
- Click All > Non-gallery application.
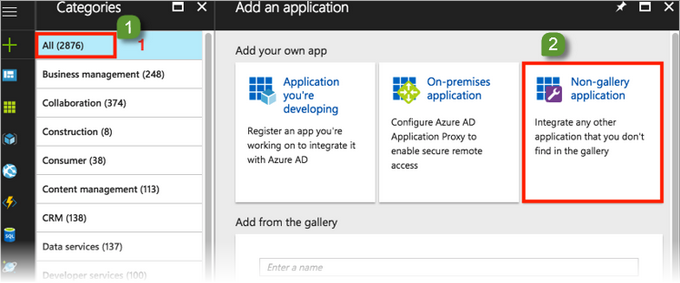
- Enter Druva inSync as the as the display name of the application and then click Add. Druva inSync gets added as an application.
- Navigate to Azure Active Directory > Enterprise Applications > All Applications and configure the Application Settings.
- Click Druva inSync Application. The application configuration page opens.
- Go to Manage > Properties and configure the settings as shown in the image below.
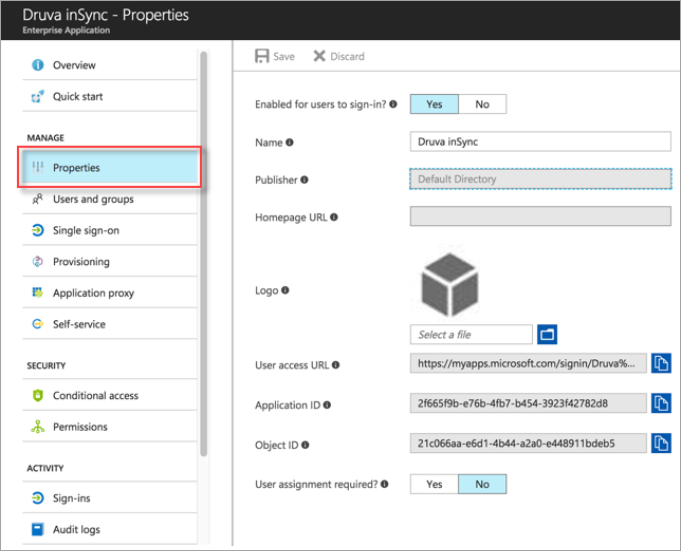
- Upload a Druva inSync Logo to identify the application easily and click Save.
Configure Azure AD single sign-on
To configure Azure AD single sign-on with Druva:
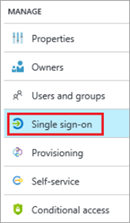
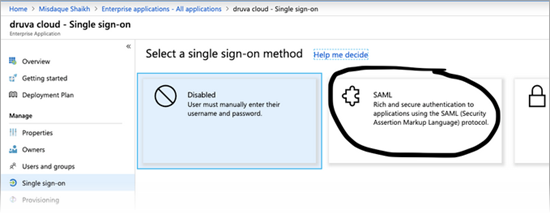
- On the Druva inSync application integration page of the Azure portal, click Single sign-on.
- To enable SSO, select method as SAML-based Sign-on on the Single Sign On window.
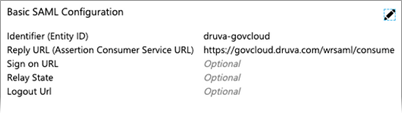
- Under the Basic SAML Configuration section, enter the following values.
Identifier: druva-govcloud
Reply URL: https://govcloud.druva.com/wrsaml/consume
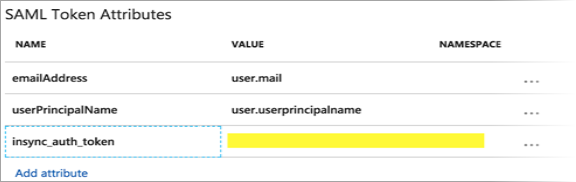
- Under User Attributes & Claims:
- Set User Identifier to user.mail.
- Select View and edit all other user attributes.
- Under SAML Attributes, delete all the attributes that are added by default.
- Add the attributes in the order specified in the table below. Ensure the order of attributes and case sensitivity of the Attribute Name is preserved.
Order Attribute Name Value 1 emailAddress user.mail 2 userPrincipalName user.userprincipalname 3 Insync_auth_token Enter the SSO token generated from inSync Management Console - Add the above attributes as follows:
- Under User Attributes and claims click Add new claim to open the Add Attribute window.
- Enter the attribute name as shown for that row.
- Enter the respective attribute value from the Value column. The token generated value is explained later in the tutorial.
- Click OK. For information on generating SSO token, see Generate SSO token.
- On the SAML Signing Certificate section, click Certificate(Base64) and save the certificate file on your system.
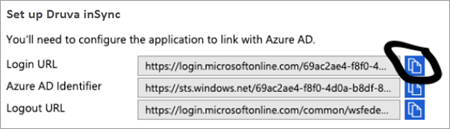
- Copy the SAML Single Sign-On Service URL from the Quick Reference section.
Configure Druva inSync GovCloud to use Azure AD login
To configure Single Sign-on:
- Log on to the inSync Management Console and go to
 > Settings.
> Settings. - Open the Single Sign-On tab and click Edit.
- On the Single Sign-On Settings window, add the following details:
- ID Provider Login URL: Enter the SAML Single Sign-On Service URL copied earlier.
- ID Provider Certificate: Open your base-64 encoded certificate in notepad and copy the content to this field.
- Clear AuthnRequests Signed and Want Assertions Encrypted.
- Click Save.
Assigning Users/Groups in Azure AD to use Druva inSync app
- On the Azure portal, open the applications view.
- Open the directory view and navigate to Enterprise applications > All applications.
- Select Druva inSync from the applications list.
- In the menu on the left, click Users and groups.
- Click Add and select Users and groups on the Add Assignment window.
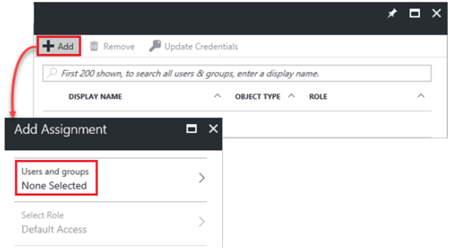
- On Users and groups dialog, select the Users or Group that you want to assign the Druva App in the Users list.
- Since Auto-provisioning the users using Azure AD is not configured, ensure that the user account selected has a corresponding account created in inSync.
- Click Select on Users and groups window.
- Click Assign on Add Assignment window.
Enable SAML in Druva inSync GovCloud
Enable Single Sign-On for the desired users from the inSync Management Console. This can be done at the profile level. Hence, it is necessary to assign the users with a profile enabled with the SSO instead of inSync Password or Active Directory.
- Login to the inSync Management Console.
- Go to Manage > Profiles and select the profile where SSO needs to be enabled.
- Go to User Privacy & Access under the General tab and click Edit.
- Under Log-in using select Single Sign On.
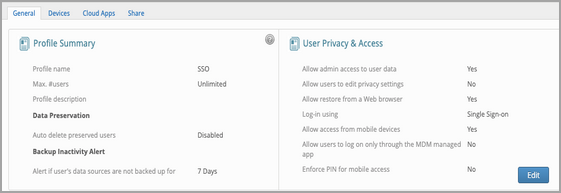
- Click Save.

