Configure Druva inSync for Microsoft 365
This topic helps new and existing users to perform the basic configuration to get started with the backup. This topic also covers advanced configuration to refer to.
Before you initiate inSync configuration to protect Microsoft 365 data, ensure the following:
- You have a Microsoft 365 global administrator account with a valid Microsoft 365 license.
- You have an Azure Active Directory Premium P1 or P2 license to assign groups to apps. For more information, see Manage access to apps.
Select the Microsoft 365 App
As a first step, you need to select the Druva app that meets your requirement:
- Advanced - Backs up the data for Exchange Online, Groups, OneDrive, Public folder, SharePoint, Teams
- Basic - Backs up the data for Exchange Online, OneDrive, Public folder, SharePoint, Teams
Use the Basic app when you want to protect this data without providing the Directory.ReadWrite.All permission. - Exchange Online & Public folder - Backs up the data for Exchange Online and Public folder
- OneDrive & SharePoint - Backs up the data for OneDrive and SharePoint
The following table explains the difference between Advanced and Basic apps.
| Supported Apps/Features | M365 Advanced | M365 Basic |
|---|---|---|
|
Exchange Online |
✅ |
✅ |
|
OneDrive |
✅ |
✅ |
|
SharePoint |
✅ |
✅ |
|
Teams |
✅ |
✅ |
|
Public Folders |
✅ |
✅ |
|
Groups |
✅ |
❌ |
|
Multi-Geo |
✅ |
❌ |
Druva app requires permissions for each app; see Microsoft 365 Permissions for Druva App.
If you are an existing user and do not want to use the Multi-Geo and Groups support features, you need to revoke access to the advanced app. No action is required if you have enabled Multi-Geo support and want to protect Microsoft Groups.
Revoke access to Microsoft 365 app
On the Re-Configure for Backup window, click ![]() and select Revoke Access.
and select Revoke Access.
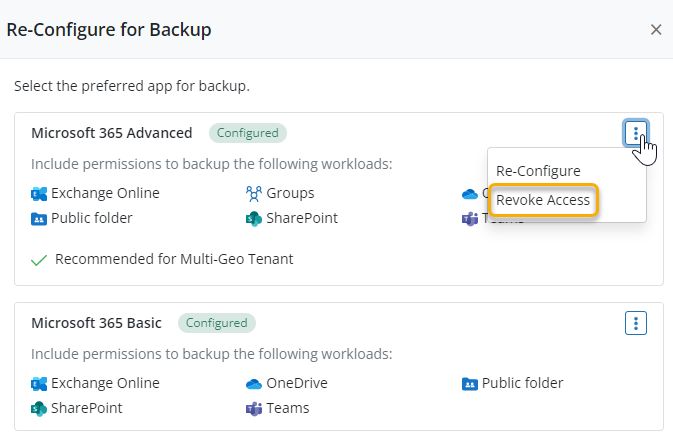
At least one other Druva app should be configured to revoke access of another app. Revoking access removes all existing permissions, restricts backup and restore of app workloads, and terminates any ongoing backups and restores associated with that app.
Check the status of app and perform the required action as listed below:
- Not Configured: Configure Microsoft 365 app
- Not Connected: Reconfigure Microsoft 365 app
- Not Licensed: Get a new license or renew the license if expired
- Connected: Configure Cloud App settings to define user attributes.
Configure inSync to protect Microsoft 365 apps
After establishing a connection with Druva to access the data to be protected, you must perform the following steps to set up Druva to protect Microsoft 365 apps.
Basic Configuration
The Onboarding Guide involves importing the users automatically and configuring the backup for users either manually or automatically by using the AD mappings. On the Overview page, click Configure Users or Configure Backup from the preferred card. The Configure Users Backup window has 2 options: Quick Configure and Auto Configure.
Quick Configure
This option enables you to manually configure the backup by assigning storage and profile to the users to be backed up. For more information, see Onboarding Guide.
Auto Configure
This option enables you to automatically configure users' backup by mapping Azure AD attributes to storage and profile. You can filter users by using Groups, Azure AD attribute, or you can import all users, and then you can assign storage and profile to the users. For more information, see Onboarding Guide.
After you configure the first backup, these are some additional tasks that you can do. Refer to the following table for details.
|
Task |
Description |
|---|---|
|
Add Microsoft 365 app users to inSync |
To start the backup of Microsoft 365 app data of users, the administrator must add or create users in inSync. inSync supports the following methods to add or create new users:
If users are already created, assign the profile that you specifically created to manage SaaS App users. To manually assign a profile to a user, see Update the profile assigned to users. |
|
Back up Microsoft 365 data manually |
As a Cloud administrator, you have an option to initiate an unscheduled backup of Microsoft 365 data as and when needed. |
|
Restore Microsoft 365 data |
Restore of data ensures that the data is available for future reference and business continuity and can be retrieved in case of accidental deletion or malicious activities. As a Cloud administrator, you can restore the Microsoft 365 data. Refer to the following links for details. |
|
Download Microsoft 365 apps data |
You can download Microsoft 365 data at custom locations such as laptops or desktops. You can perform a download of entire Microsoft 365 apps data or selective downloads of specific data residing within Microsoft 365 apps. Refer to the following links for details. |
|
Monitor Microsoft 365 data |
You can monitor all the activities related to backup and restore by using alerts, logs, reports, and audit trails.
|
Advanced Configuration
After you have started the backups, there are some advanced configurations that you can consider. Refer to the table below.
|
Configuration |
Description |
|---|---|
|
Multi-Geo |
With this feature, you can protect data for Microsoft 365 Multi-Geo enabled tenants. You can also assign storage to users based on their geo-location. For more information about multi-geo support, see the following articles. |
|
Data lock |
You can enable Data Lock to prevent modification, deletion, or tampering of business-critical data and make it immutable. For more information, see Data Lock. |
|
User provisioning |
Druva offers different approaches to configure inSync for user provisioning. For more information, see Configure inSync for user provisioning. |
| Azure Active Directory (AD) Conditional Access policies |
Druva validates the Conditional Access policies enabled for your Microsoft 365 tenant during the Microsoft 365 app configuration to authenticate and provide conditional access to users. |
| Configure SaaS Apps settings for Microsoft 365 | Define the user attribute that you want inSync to use to map user account to their Microsoft 365 app account. For more information, see Configure SaaS Apps settings for Microsoft 365. |
| Get user data encryption key(ekey) |
To ensure that the Microsoft 365 data that is backed up is secure, you must configure inSync to get the data encryption key(ekey). For more information, see Get user data encryption key (ekey). |
| Configure a profile to protect Microsoft 365 app data |
To back up Microsoft 365 app data, you must specify the Microsoft 365 backup settings in an existing profile or in a new profile. For more information, see Configure a profile to protect Microsoft 365 app data. |
Reconfigure Microsoft 365
Reconfiguration of the Microsoft 365 app is required in the following scenarios:
- Discover a new Cloud App that is added to inSync.
- For any permissions related updates required by inSync app in Microsoft Azure.
- Any permission-related changes that are made to the global administrator account used to configure an Microsoft 365 app in inSync.
Example: If any changes are made to the conditional access permissions of the global administrator account used to configure any Microsoft 365 app, you must reconfigure Microsoft 365 account in inSync.
Note: When you reconfigure Microsoft 365, inSync stops all the ongoing cloud app backups.
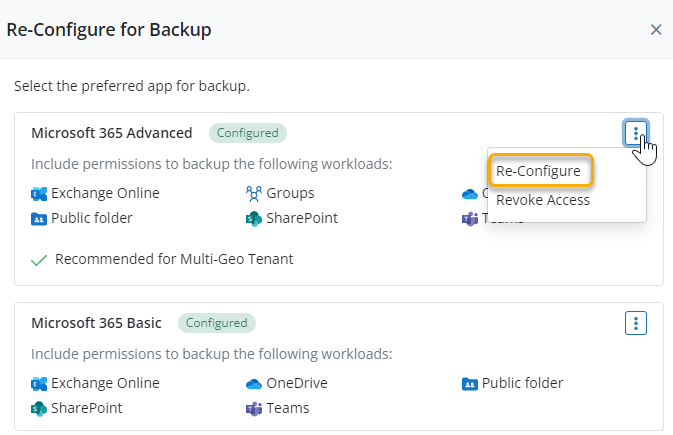
To reconfigure inSync with Microsoft 365:
- Sign in to inSync Management Console and navigate to Microsoft 365.
- On the Overview page, click Re-Configure.
- On the Re-Configure for Backup page, click
 > Re-Configure besides the app type that you want to reconfigure.
> Re-Configure besides the app type that you want to reconfigure.
Note: The Microsoft 365 tenant must be the same for all the sub-apps you would like to configure. Configuring sub-apps for Microsoft 365 in multiple tenants is not supported.
- On the confirmation pop-up, click Re-Configure to proceed with reconfiguration.
- On the Microsoft 365 login page, enter the Microsoft 365 global administrator's user name and password, and then click Sign in.
- Click Accept to grant inSync app the required permissions to access Microsoft 365 data.
- The permissions displayed are a combined list for all Microsoft 365 apps. If you want to know more about specific permissions applicable for each app, see Microsoft 365 Permissions for Druva App.
inSync gets connected to Microsoft 365 data of all users in your organization.
Verify Configuration
After you complete the configuration of inSync with Microsoft 365 app, you can use the Verify Configuration option to check if inSync can access your users.
To verify the configuration:
- Sign in to inSync Management Console and navigate to Microsoft 365.
- On the Overview page, click
and then click Verify.
- In the Verify Configuration dialog, select the app for which you want to verify the configuration.
Based on the selection of the app, the options to verify the configuration are displayed. The following image displays options when Microsoft 365 app is selected.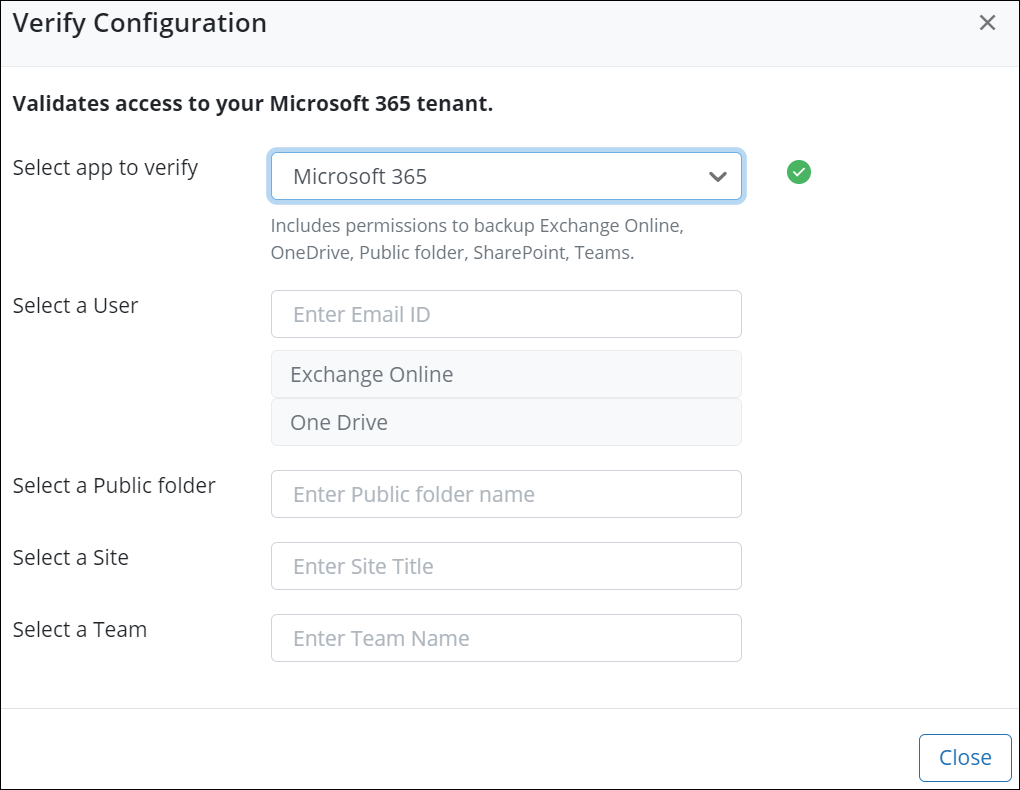
Here is the list of parameters for each sub-app to verify the configuration:- Exchange Online and OneDrive: Email ID of the user
By default OneDrive is mapped to the Username parameter in Microsoft 365, which cannot be changed. If the email ID and UPN are different in Microsoft 365 tenant then OneDrive backup will fail. - SharePoint: Site title
- Teams: Team Name
- Public folder: Public folder name
inSync recommends that you enter an organization user email address to check if the configuration works instead of an administrator user.
- Exchange Online and OneDrive: Email ID of the user
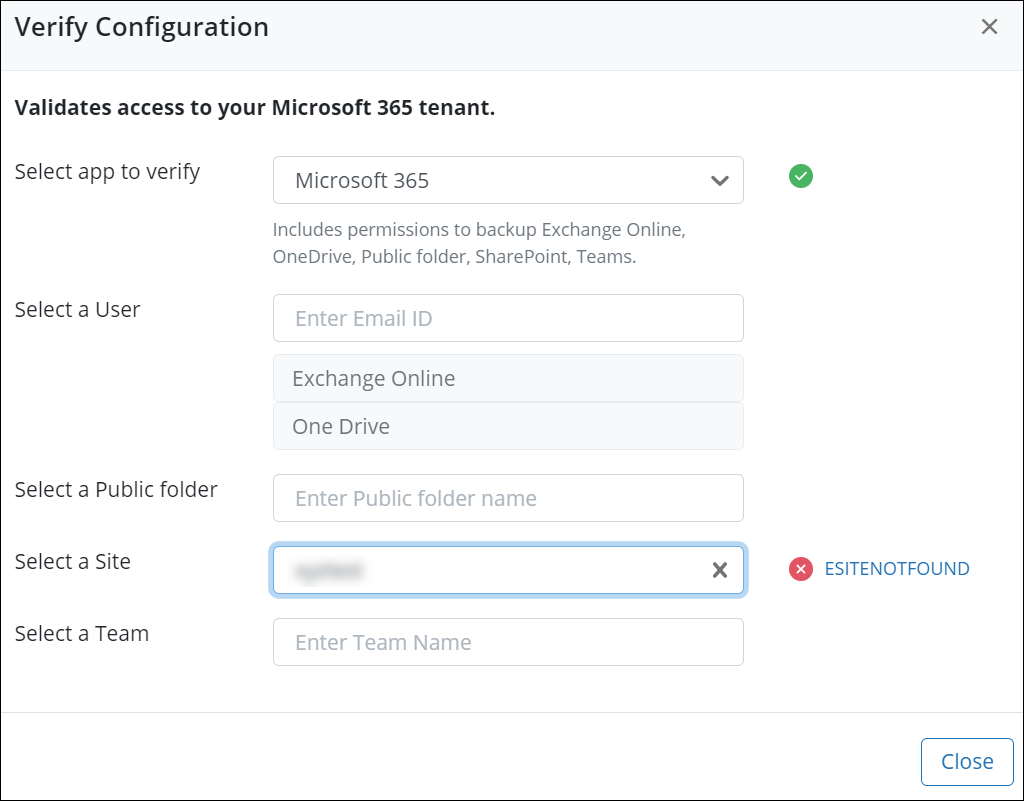
- When you select an app and provide the parameters for verification, inSync performs the following checks as a part of verification:
App authentication: This step checks if inSync can utilize the available refresh tokens to validate the connection with the Microsoft 365 tenant.
User and user's M365 Exchange Online & OneDrive devices: This step checks if the user exists at the Microsoft 365 end. - If any of the authentication steps fail for the selected app, you are prompted with an error message. Click the error message to view the error details.
Next Steps

