Unable to generate reports on CloudRanger
Problem description
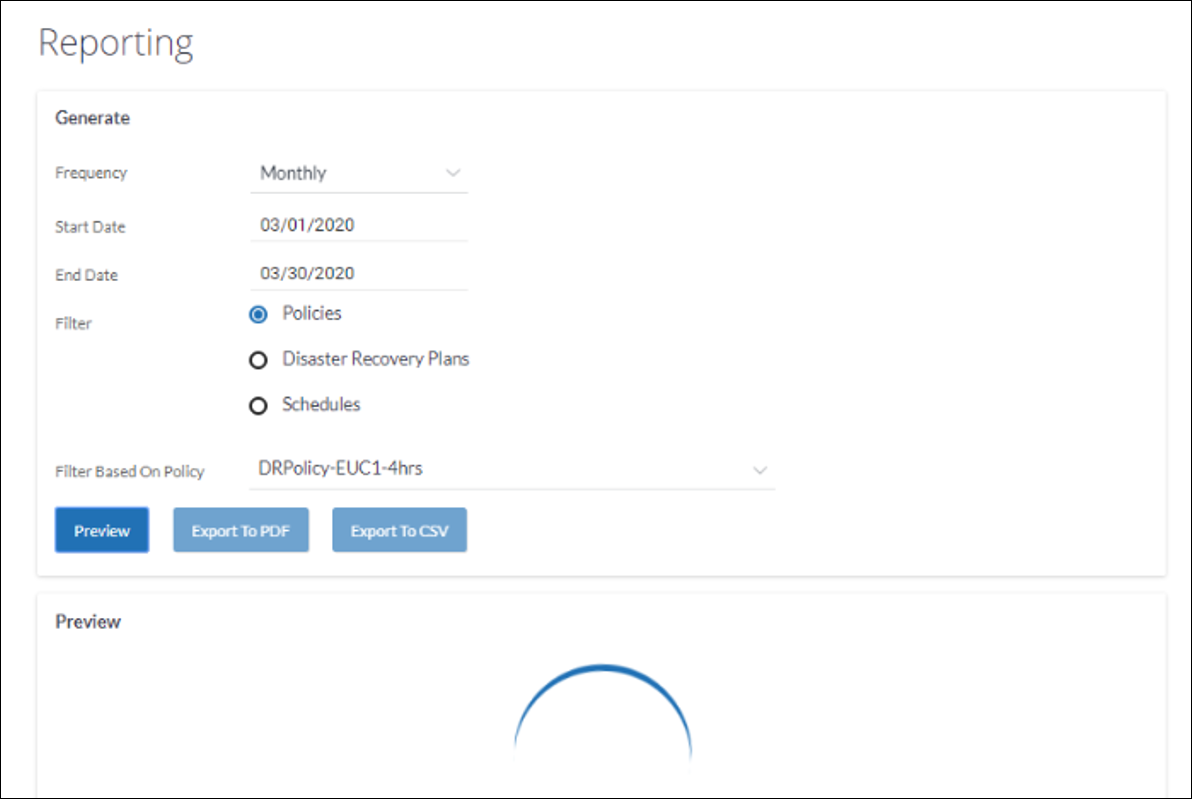
When attempting to generate a report on the Druva CloudRanger admin console, the report beings to load up but never proceeds to generating it.
Cause
The cloud formation stack is incorrectly updated/removed/deleted.
Druva CloudRanger provides a CloudFormation template that is used to create a stack. The CloudFormation stack generates the following IAM permissions for Druva CloudRanger to access your AWS Account:
- IAM Role
- IAM Instance Profile
- IAM Policy
The generated Amazon Resource Name (ARN) of the IAM role is then linked back to CloudRanger so that it can run backup and restore jobs on your AWS workloads. For more information, please see Create an AWS Access Role.
Note: Druva CloudRanger follows all security protocols and best practices recommended by AWS. All access permissions to your AWS resources and regions are controlled by AWS Identity and Access Management.
Resolution
To update AWS access permissions:
- On your Druva CloudRanger console, click the Settings icon to navigate to Account Settings.
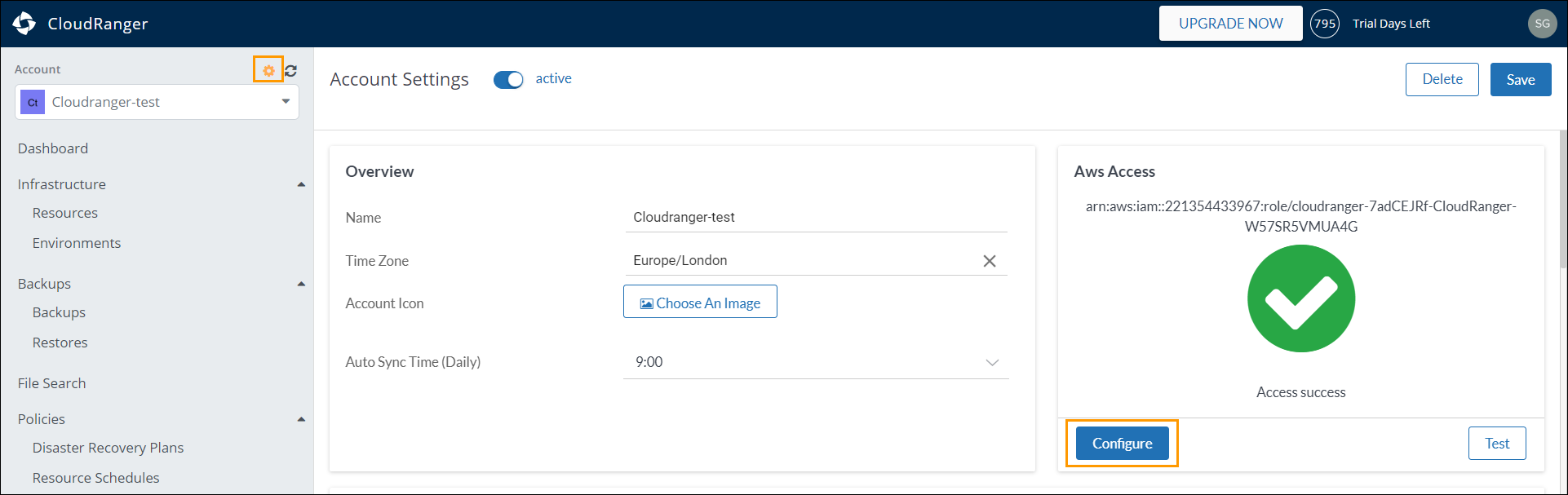
- Click Configure under AWS Access. Copy the CloudFormation URL.
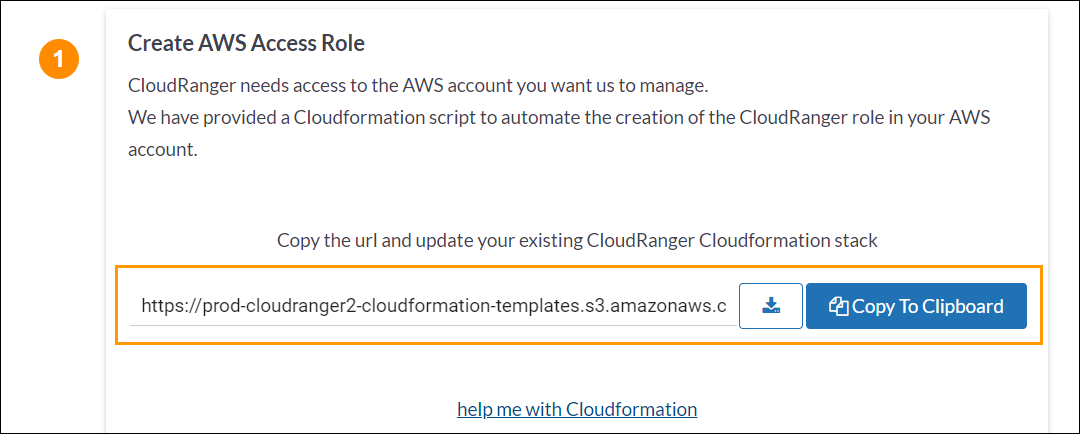
For step-by-step instructions on CloudFormation, you may click help me with Cloudformation.
- Login to your AWS Console and navigate to the CloudFormation page.
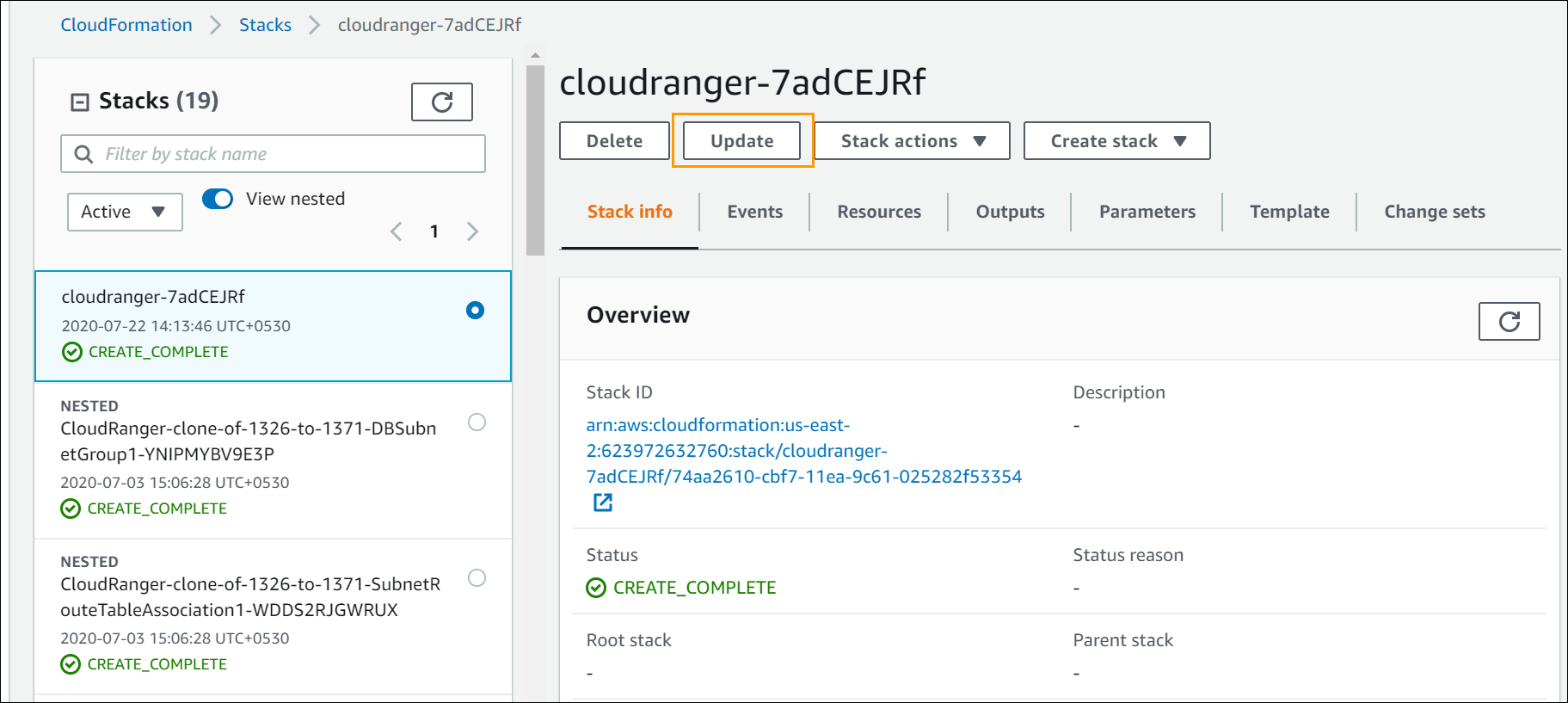
- Select the stack that you previously created when configuring CloudRanger, and then click Update.
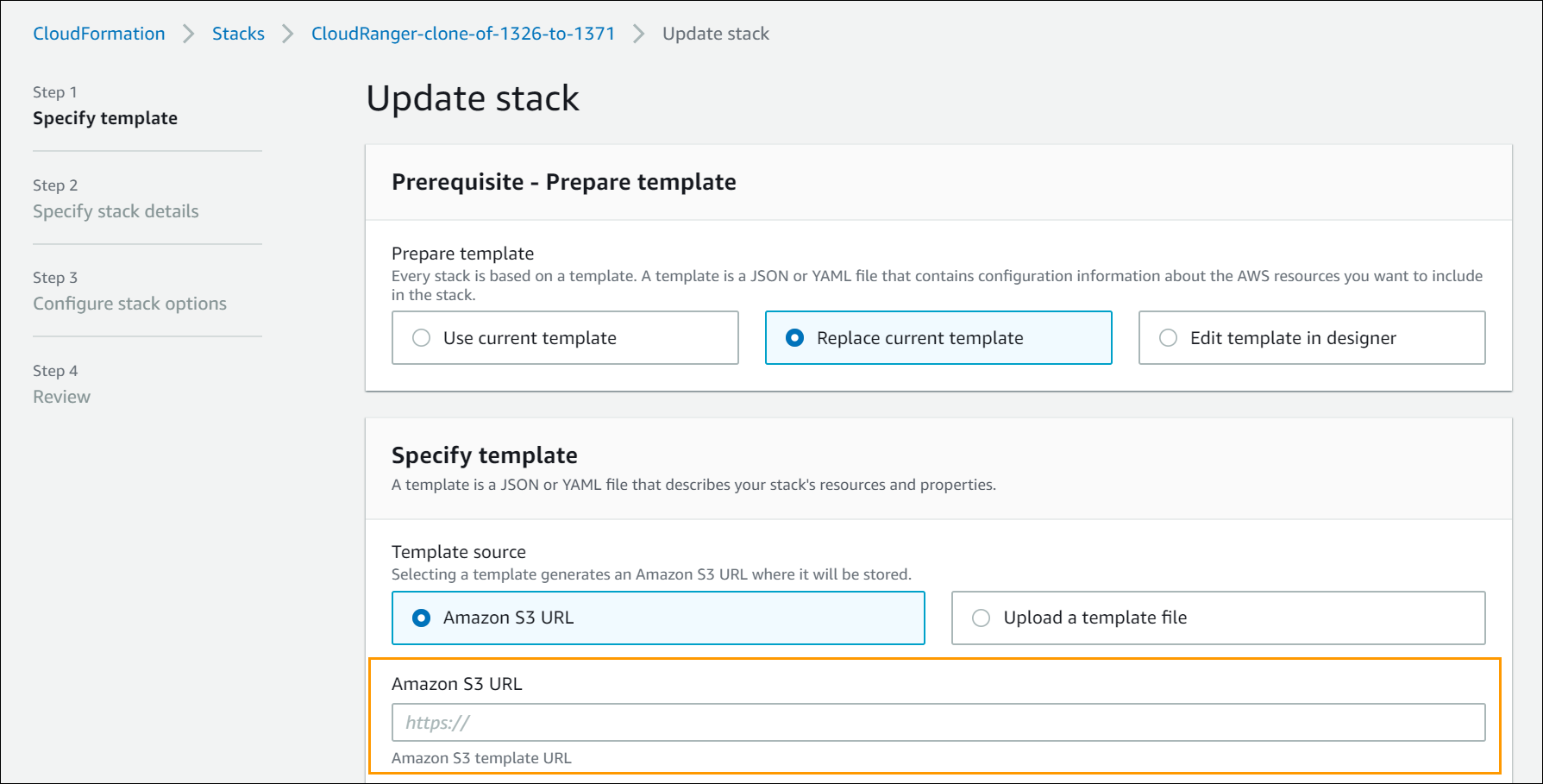
- On the Specify template page, select Replace current template. Then paste the CloudFormation URL into the Amazon S3 URL text box. Click Next.
- Click Next on the Specify stack details and Configure stack options pages.
You will be able to preview the changes before you click Update stack to confirm the CloudFormation changes to resources.
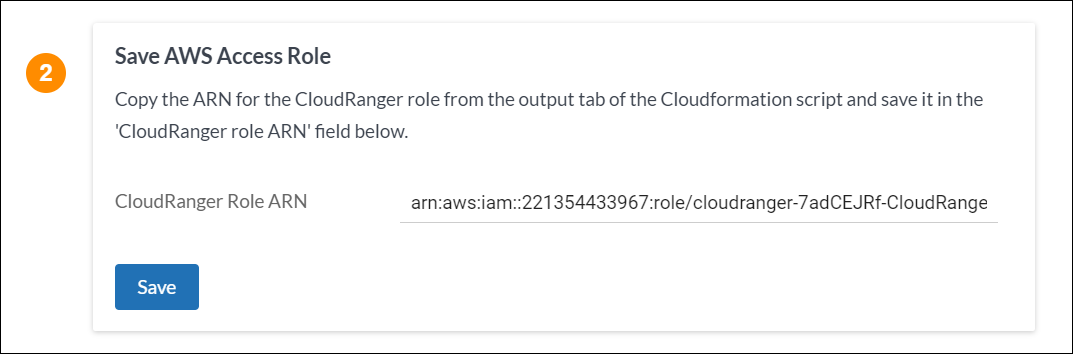
- Once the stack update is complete, navigate back to CloudRanger, and click Save under Save AWS Access Role.
Your IAM role and AWS account access should now be updated with the latest permissions, allowing you to take advantage of any new functionality that is released.

