About Maas360 by IBM
Overview
From iOS 7 onwards, Apple has allowed MDM (Mobile Device Management) solutions to pass dictionaries directly in the applications, that can be downloaded through MDM. This functionality is supported by MaaS360. The dictionary reference contains settings that can be defined via MDM. The MDM enrollment setup skips all the prompts and user intervention for installation and activation of the Druva Mobile App. This ensures that each user undergoes the same set of steps when enrolling their iOS devices. For example, the dictionary contains configuration information about the server address, email address of the user, mass deployment token that is required for authenticating the user, and security information like allow or restrict copy, printing of files, and allow or restrict opening the files in different apps.
inSync uses App Configuration for Enterprise to support the Druva Mobile App for iOS devices with MaaS360. Many applications require users to enter URL, port, email address, and various configurations as part of a one-time setup of an application. These manual configurations can impact the adoption and success of an organization’s mobile app initiatives, increase the burden on a help desk fielding calls from users, and adds the burden of maintaining documentation that needs to be updated frequently as new updates to the application are made available.
Apps commonly implement the following types of configurations:
- Backend service configuration: URL, port, use SSL, group/tenant code
- User configuration: username, email, domain
As a inSync user, all you have to do is enroll the iOS device, and install the Druva Mobile App from MaaS360. In quick and easy steps, you can install and monitor the Druva Mobile App on all iOS user devices in your organization. This allows you to have complete visibility of all iOS devices in your organization on which the Druva Mobile App is installed.
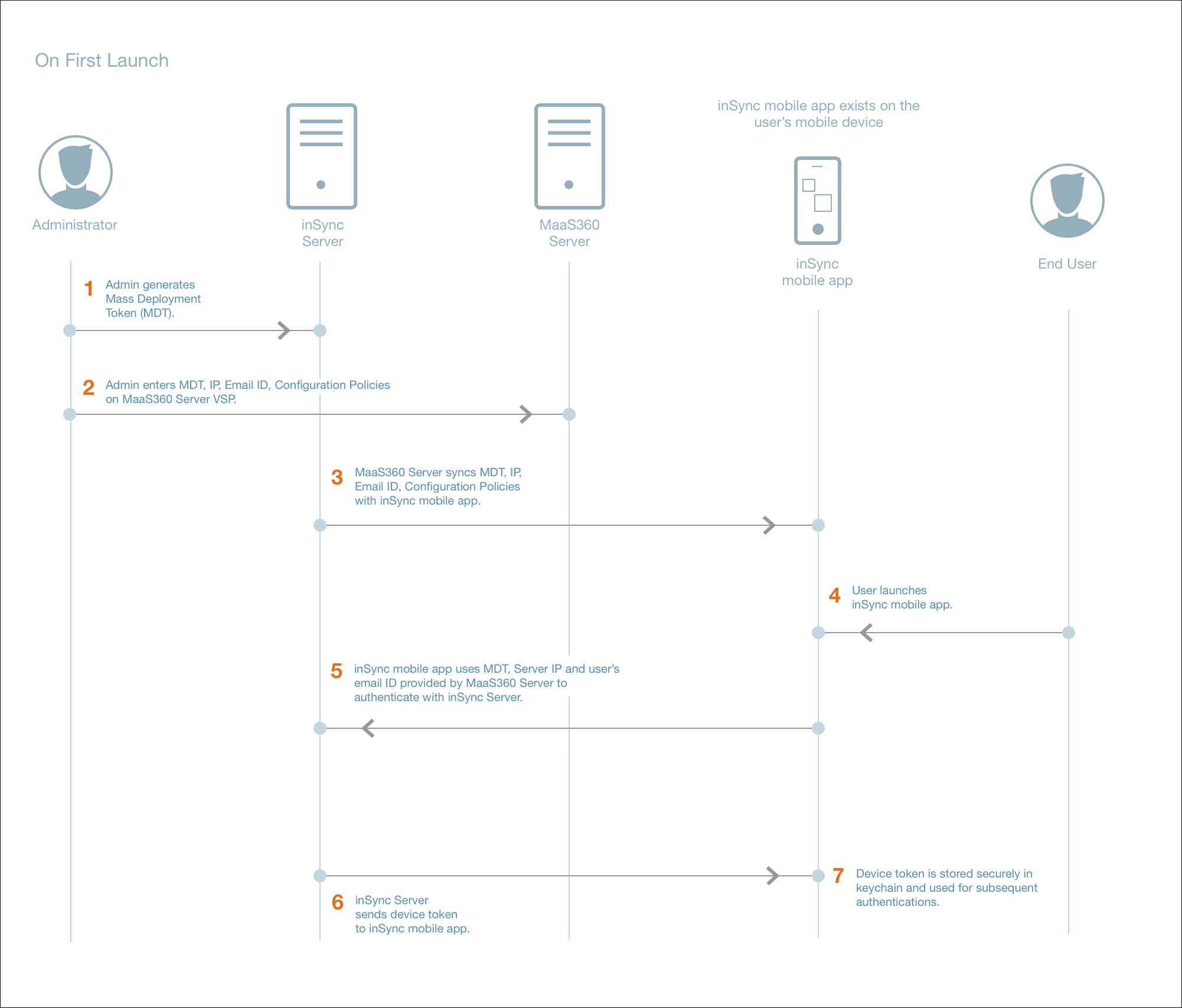
Workflow when the Druva Mobile App is launched for the first time
| Task no. | Task |
|---|---|
| 1. |
Administrator generates the mass deployment token from the inSync Management Console. The mass deployment token allows you to distribute and silently activate the Druva Mobile App on multiple iOS devices. For generating the mass deployment token, see generate a mass deployment token. |
| 2. |
Administrator executes the following tasks, and provides the information to MaaS360 Server:
|
| 3. |
MaaS360 Server syncs the mass deployment token, IP address, user's email ID, and configuration policies with the Druva Mobile App. |
| 4. |
inSync user launches the Druva Mobile App on the iOS device. |
| 5. | Druva Mobile App uses mass deployment token, Server IP, and user's email ID provided by MaaS360 Server to authenticate with inSync Server. |
| 6. |
inSync Server sends device token to Druva Mobile App. |
| 7. | The device token is saved securely in the iOS's keychain and is used for subsequent authentication. |
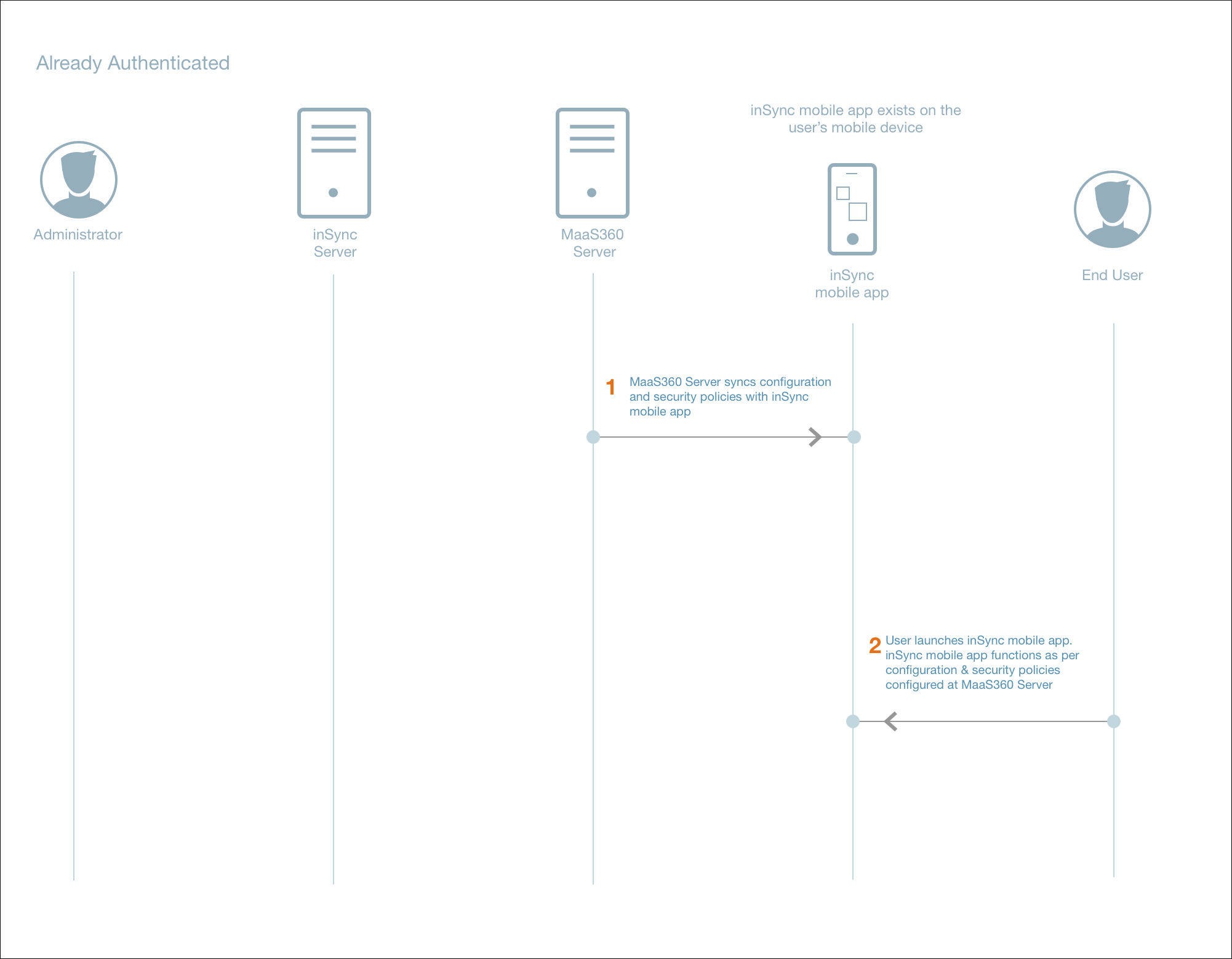
Workflow when the Druva Mobile App is already authenticated
| Task no. | Task |
|---|---|
| 1. | MaaS360 Server syncs the mass deployment token, IP address, user's email ID, and configuration policies with the Druva Mobile App. |
| 2. | inSync user launches the Druva Mobile App on the mobile device. The Druva Mobile App functions per the configuration and security policies that are configured at the MaaS360 Server. |
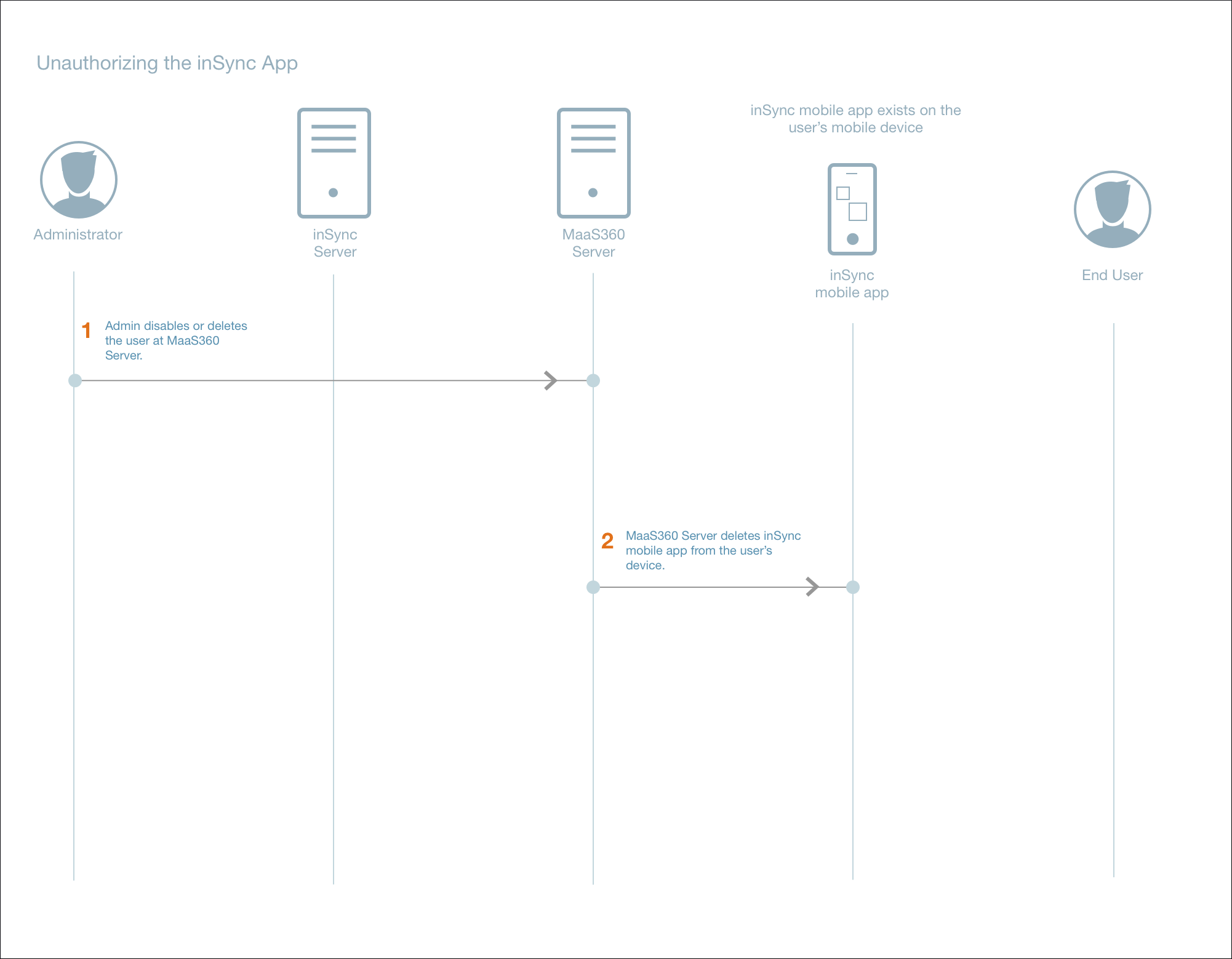
Workflow when the Druva Mobile App is unauthorized
| Task no. | Task |
|---|---|
| 1. |
From the MaaS360 console, the MaaS360 administrator will disable or delete the user at the MaaS360 Server. |
| 2. |
When the user is deleted from MaaS360, then the Druva Mobile App that is on the user's device will be unauthorized. Additionally, the MaaS360 Server will automatically delete the Druva Mobile App from the user's iOS device. |
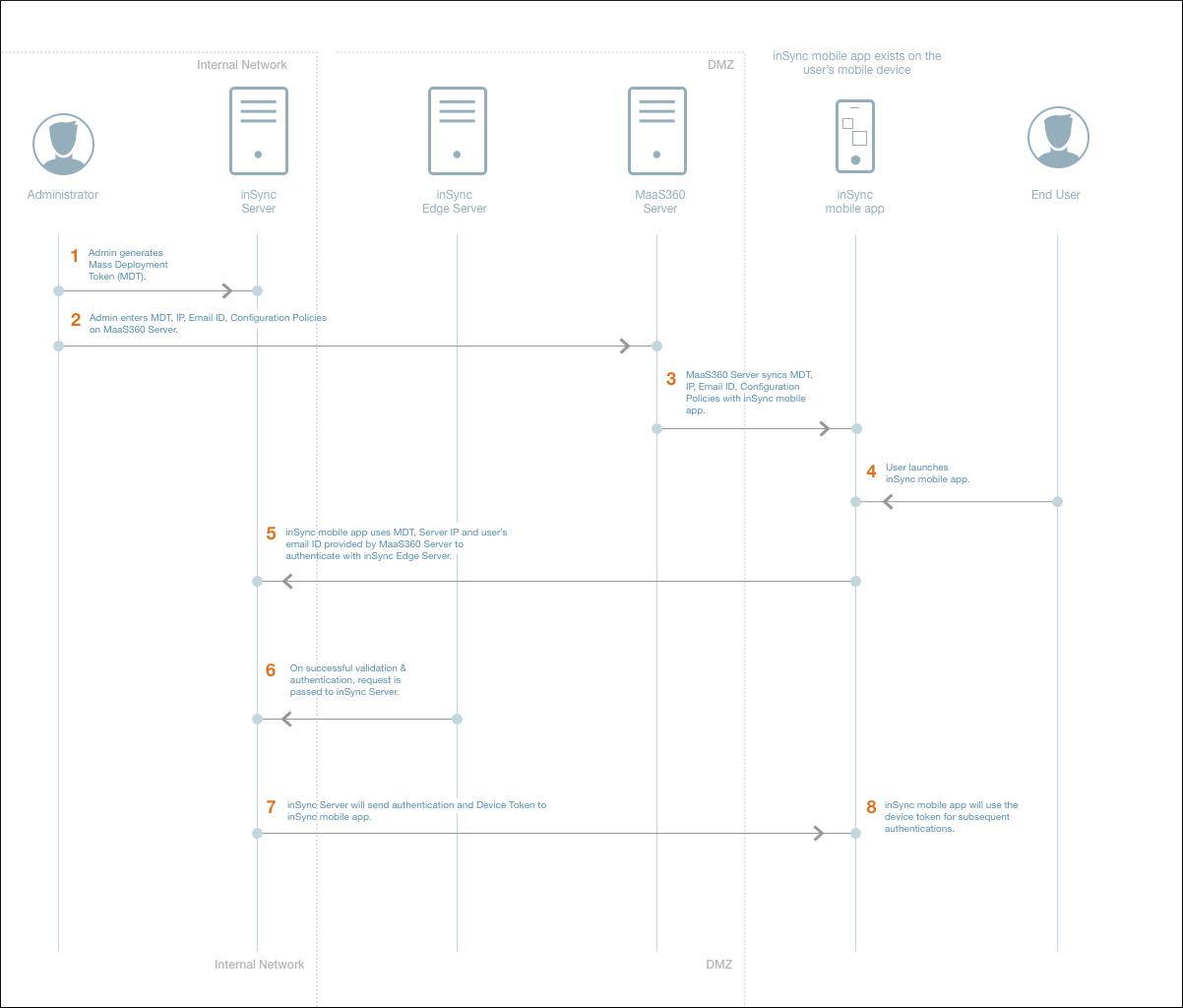
Workflow when the Druva Mobile App is launched for the first time in inSync On-Premises with Edge Server
| Task no. | Task |
|---|---|
| 1. |
Administrator generates the mass deployment token from the inSync Management Console. The mass deployment token allows you to distribute and silently activate the Druva Mobile App on multiple iOS devices. For generating the mass deployment token, see generate a mass deployment token. |
| 2. |
Administrator executes the following tasks, and provides the information to MaaS360 Server:
|
| 3. |
MaaS360 Server syncs the mass deployment token, IP address, user's email ID, and configuration policies with the Druva Mobile App. |
| 4. |
inSync user launches the Druva Mobile App on the iOS device. |
| 5. |
Druva Mobile App uses device token, Server IP, and user's email ID provided by MaaS360 Server to authenticate with inSync Edge Server. |
| 6. |
On successful authentication and validation, the request is passed to inSync Server. |
| 7. |
inSync Server sends the authentication and device token to Druva Mobile App. |
| 8. | Druva Mobile App will use the device token for subsequent authentication. |
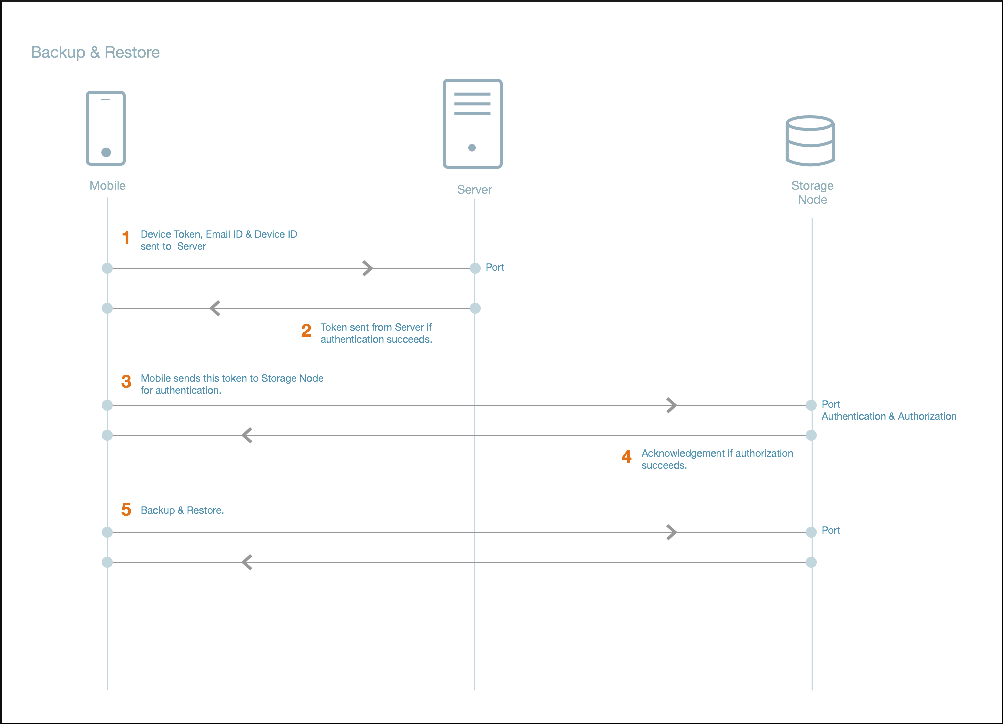
Backup and restore workflow for Druva Mobile App