Upcoming Enhancements for Druva Console Login
The following updates will be available for Public Cloud and Phoenix Gov Cloud starting:
- 13th April, 2023 for APAC AWS Regions
- 20th April, 2023 for Rest of the World AWS Regions
End of Support for Email-based Multifactor Authentication
As a security best practice, we will no longer support Email-based Multifactor Authentication.
Action Required: For a smooth transition, configure Authenticator App-based or SMS-based Multifactor at the earliest. Learn More
Note: If you miss changing your Multifactor Authentication method, we will configure your account to use Authenticator App-based Authentication as part of the update.
Mandating Multifactor Authentication
As a security best practice, we will now mandate Multifactor Authentication.
Action Required: For a smooth transition, configure Authenticator App-based or SMS-based Multifactor at the earliest. Learn More.
Note: If you miss setting a Multifactor Authentication method, we will configure your account to use Authenticator App-based Authentication as part of the update.
Frequently Asked Questions
After this update, when we configures my account to use Authenticator App-based Authentication, can I change it later?
You can change the Multifactor Authentication anytime. Refer to the product documentation.
What happens if I am using an email alias for login?
After this update, email aliases will not be supported. You will need unique login credentials and separate devices for each administrator to log in.
Will this change impact me even if I have configured SSO?
No. This change will not impact customers who have configured SSO. This change is applicable only for password logins, including failsafe administrators.
Is Multifactor Authentication required with Single Sign-on (SSO)?
No. Multifactor Authentication is not required with Single-Sign on. Refer to the product documentation.
How can other administrators in my organization login into the Druva Console after Multifactor Authentication is enabled?
- For Authenticator App-based Authentication:
- At the first login, link to the authenticator app by scanning the QR code.
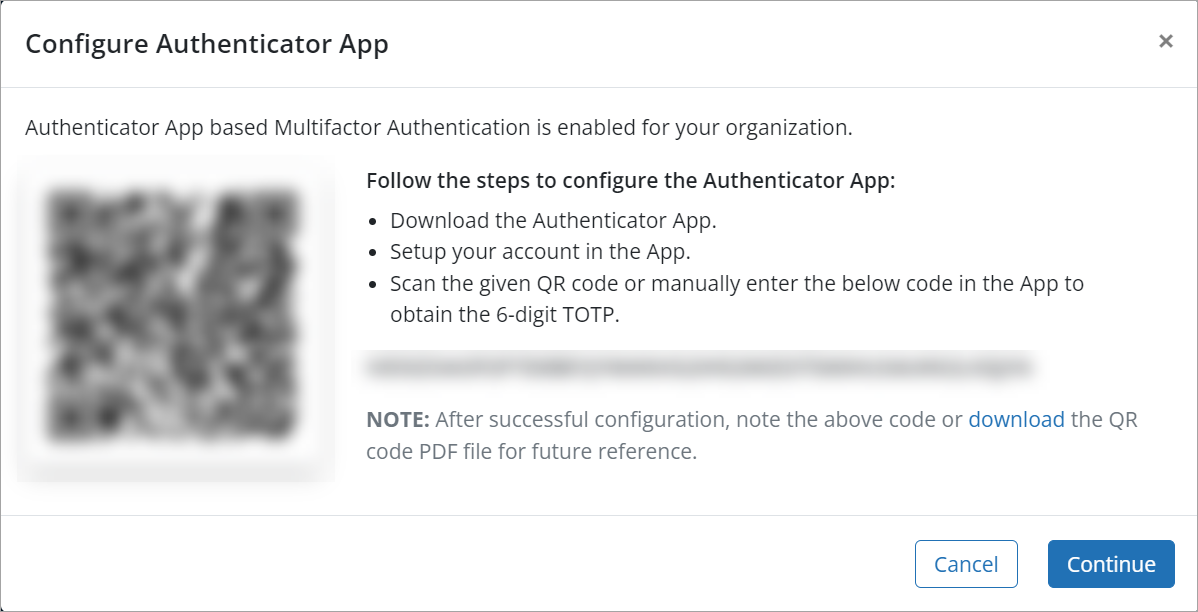
2. Enter a QR code in the authenticator app and click Verify.
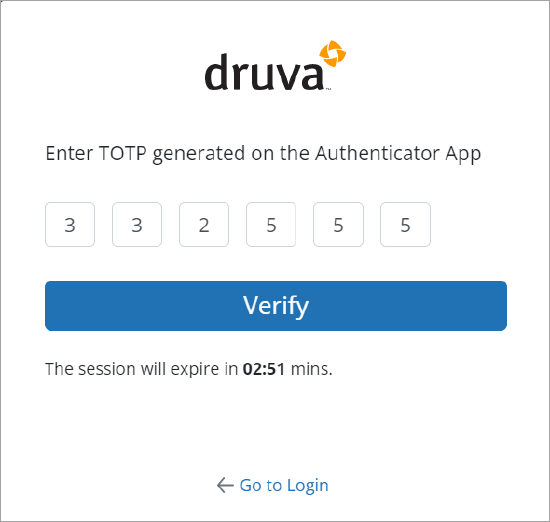
At every next login, the administrators are required to authenticate themselves using the OTP they receive via the authenticator app.
- For SMS-based Authentication:
- At the first login, Register your mobile number to receive the OTP.
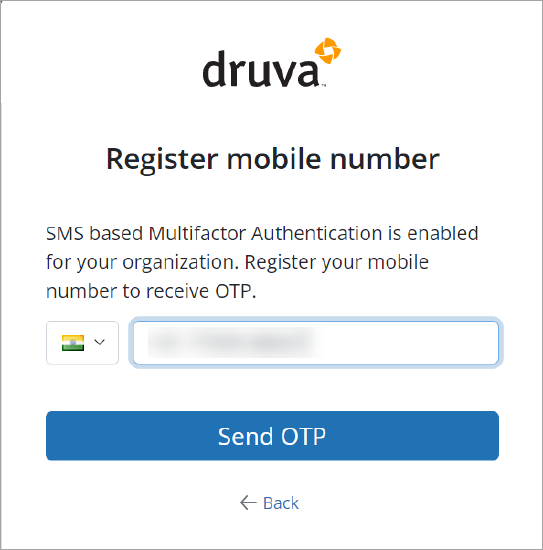
2. Enter the OTP and click Verify.
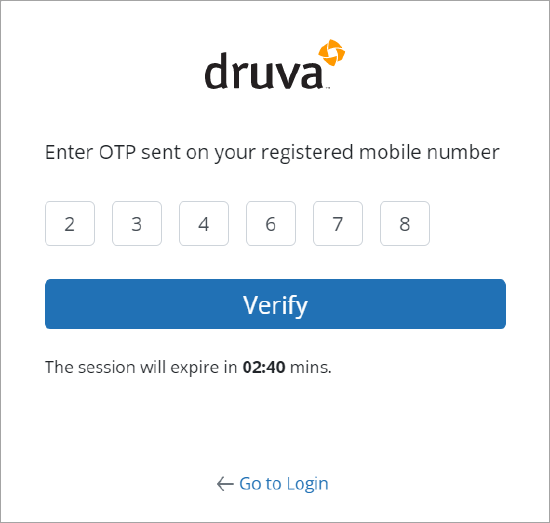
At every next login, the administrators are required to authenticate themselves using the OTP they receive on their mobile devices.
What should I do if I change my mobile device or the authenticator app?
You can ask another DCP administrator to reset the Multifactor Authentication. Refer to the product documentation.
What if an administrator doesn't receive OTP?
You can contact support.

