About Sensitive Data Governance
What is Sensitive Data Governance?
Sensitive Data Governance provides visibility of compliance breaches associated with end-user data in your organization. Sensitive Data Governance lets you proactively track, monitor, and get notified for data compliance risks in your organization.
The end-user data can be across any of the following data sources:
- Endpoints such as laptops, desktops, iOS and Android devices
- OneDrive from Microsoft 365 services
- Emails that are backed up from Gmail and Exchange Online
- Google Drive
Sensitive Data Governance reports compliance violations for sensitive data that occurs in the email body, subject, and attachments. inSync displays emails with sensitive data on the Sensitive Data Governance Dashboard and allows administrators to download emails in the EML file format.
Once enabled, Sensitive Data Governance:
- Provides the ability to define sensitive data and scan user data for compliance violations or risks of violations.
- Allows you to locate end-user data that has violated a compliance policy.
- Lets you generate a non-compliance report and view the visual representation to indicate adherence to compliance regulations in your company. For more information, see Non-Compliant File Report and Non-Compliant Email Report.
Notes:
- inSync scans the data for violations once a day and reports violations on the latest version of a file or email .
- Sensitive Data Governance does not check for violations in unattached PST files, calendar events, and contacts data that are backed up from Exchange Online and Gmail.
- Sensitive Data Governance scans the following archive file types: *.zip, *.tar, *.tar.gz, *.tar.bz2. However, you must enable scanning of archive files from Compliance Settings. For more information, see Modify Compliance Settings.
- Sensitive Data Governance will detect violations in emails backed up from Exchange Online and Gmail starting from the last backup after this capability is available. For example, James has purchased a Sensitive Data Governance Add-On service and is backing up data daily starting from 1 January 2016. He is also monitoring the data for sensitive information and potential data risks. If the capability to check for violations in emails backed up from Exchange Online and Gmail is available on 21 March 2016, then Sensitive Data Governance will detect violations in the emails starting from backups on 20 March 2016.
What are the benefits?
Sensitive Data Governance (SDG) provides the following capabilities:
- Centralized Sensitive Data Governance Dashboard: The Sensitive Data Governance Dashboard provides an easily navigable federated view by file name, modified on, user ID, sensitive data matched, and policy violated. This dashboard lets you quickly access and track compliance violations.
- Non-compliance reporting: You can subscribe to the non-compliant reports, which are automatically generated and emailed to subscribers when potential data risks are discovered.
- Predefined, customizable compliance templates: You can select from predefined templates such as HIPAA, GLBA, PCI, or customize templates. inSync will automatically scan, identify, and alert the organization of risks.
- Intuitive Dashboard, Simplified Administration, and Powerful Admin Controls
- Access to a simplified dashboard with a dedicated file and email view with complete details of violations for every file version and email conversation in their enterprise.
- Dedicated Non-Compliant report for emails for offline review and investigations.
- Tamperproof audit trails with complete visibility of administrative changes to compliance policies.
- Thresholds for each sensitive data to immediately act on critical violations.
- Ability to scan files based on MIME types to cover against rogue or malicious end users trying to change extensions of files with sensitive data.
- Take actions to resolve compliance violations as per your Incident response process
- Ability to take resolve violations and quarantine violations which will disable downloads and restores of files and email for inSync end users from inSync Web.
- Support for more regions and pre-defined templates
- Support for sensitive data relevant to US, UK, Germany, Australia, and South Africa as well as sensitive data classified as per global regulations.
- Download files or Emails for Offline review
- Ability for administrators to download files and emails for offline review before taking remedial actions and avoid potential data breaches.
What are the components of a compliance policy?
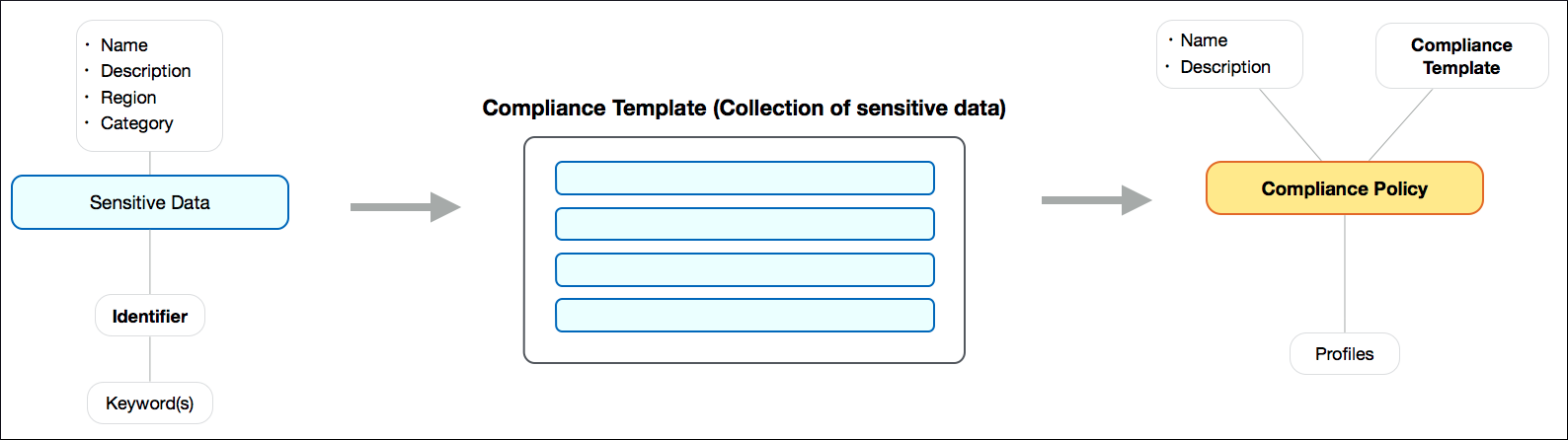
The following illustration provides information about the components of a compliance policy:
Is Sensitive Data Governance available for my inSync Cloud setup?
Sensitive Data Governance is available as an Add-On service on top of the available inSync Cloud editions-Business, Enterprise, and Elite. To purchase Sensitive Data Governance Add-on service for your organization, contact Druva Sales.
Who can access Sensitive Data Governance capabilities?
The cloud administrator can do the following:
- Create, modify, and delete compliance policies.
- View the compliance summary at the Compliance Dashboard.
- Access the Non-Compliant report for all the profiles.
Profile administrators can do the following:
- Access the Non-Compliant report only for the profiles that they are mapped to. However, they cannot view the Sensitive Data Governance summary at the Sensitive Data Governance Dashboard.
What happens if I do not have a valid Sensitive Data Governance license?
If Sensitive Data Governance Add-on service is not available
If you do not have Sensitive Data Governance Add-on service, then you will not be able to access Sensitive Data Governance. Instead of the Sensitive Data Governance Dashboard, you will see a message requesting you to contact Druva Sales.
If Sensitive Data Governance Add-on service is expired
inSync will stop indexing data for all inSync users once the license expires. Additionally, cloud administrator will not be able to create, view, modify, or delete compliance policies, compliance templates, and sensitive data. However, inSync will retain the non-compliant violation information. Additionally, the non-compliant reports will not be displayed.
For more information, see Frequently asked questions.
What can I do if a policy violation is detected?
- Generate Non-Compliant File Report and Non-Compliant Email Report
You should generate the Non-Compliant File Report and Non-Compliant Email Report to identify the user, data sources, and files that violate your organization’s compliance policy. These reports will help you investigate potential risks well in advance of a data breach. These reports also
help you to get in touch with the respective end users to get them to protect their sensitive data. For more information, see Generate report. - Put the user on Legal Hold
Based on the investigations conducted on the basis of the Non-Compliant report, you may choose to place the relevant users on Legal Hold within inSync, if they are found to work with sensitive data that is not in compliance with your company policy. For more information, see Create a Legal Hold policy.