About Audit Trails
Introduction
Audit Trails captures the activities performed by the administrators in the console and logs it. It is useful for organizations to meet the data governance and compliance requirements by providing a chronological view of all the administrator activities.
Druva Cloud Administrators can track and monitor all the activities ensuring complete transparency, traceability, and accountability of all the administrators, thereby aiding forensics and compliance initiatives.
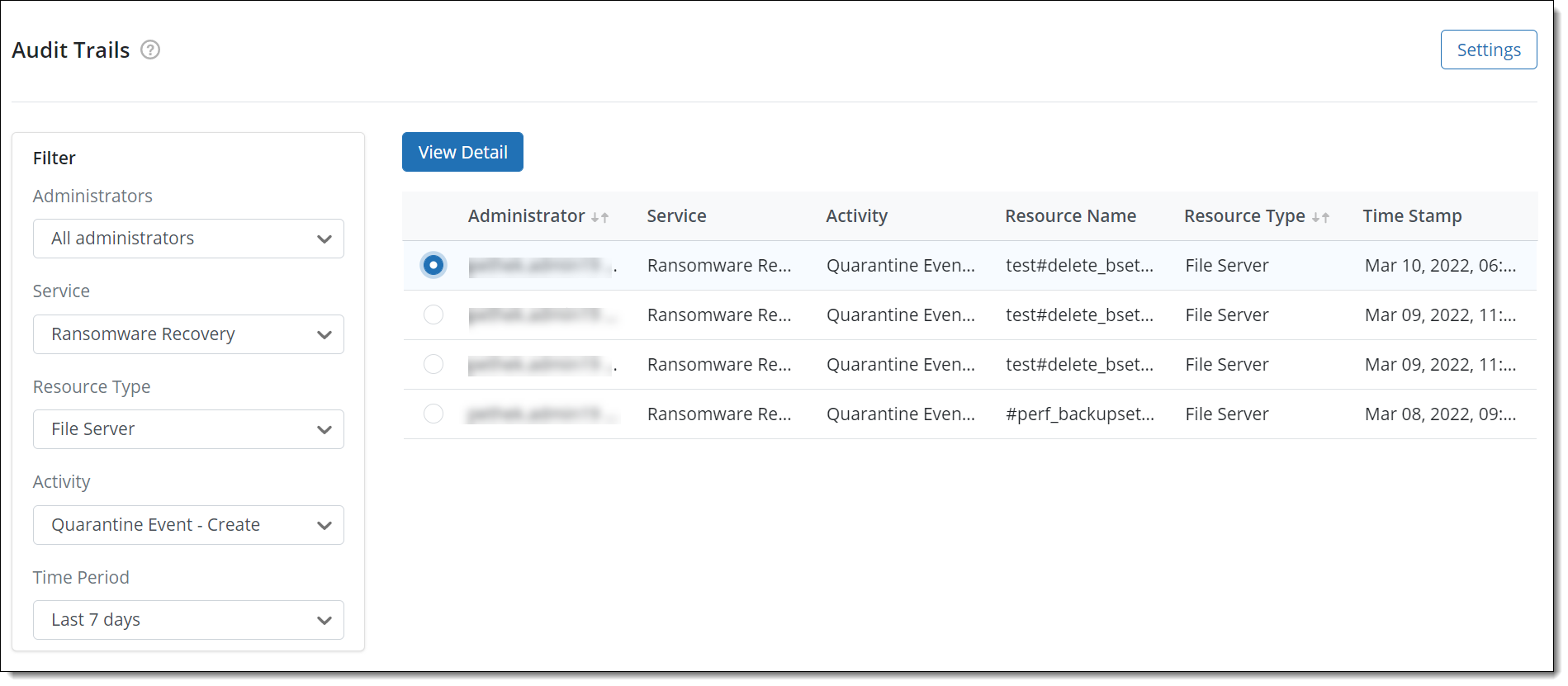
Audit Trails captures the following information about an activity performed -
- The name of the administrator who performed the activity
- The name of the Druva Service in which the activity was performed
- The activity that was performed
- The name of the resource on which the activity was performed
- The Resource type
- The time stamp in, MMM-DD-YYYY HH:MM:SS format, when the activity was performed
Druva Cloud Administrators can also apply filters and generate a view for specific administrators, service, activity type, and so on. For more information, see Filter Audit Trails.
Benefits
Apart from the Governance and Compliance reasons, Audit trail enables Druva Cloud Administrators to:
- Monitor and control the activities of all administrators.
- Diagnose erroneous and critical activities performed by administrators.
- Select resources and their specific entities and generate reports for audit.
View Audit Trails
Audit Trails is available only from the Ransomware Management Console.
To view Audit Trails
- Open a web browser.
- Access the Druva Cloud Platform Console using the URL https://login.druva.com.
After login, you are redirected to the Druva Cloud Platform Console dashboard page. For detailed information, see Introduction to Druva Cloud Platform Console. - Scroll-down until you see the Ransomware Recovery section and then click on any of the available service. Example - Ransomware Recovery
You are redirected to the Ransomware Recovery Management Console. - On the Ransomware Recovery Management Console menu bar, click Audit Trails.
View Audit Trail Details
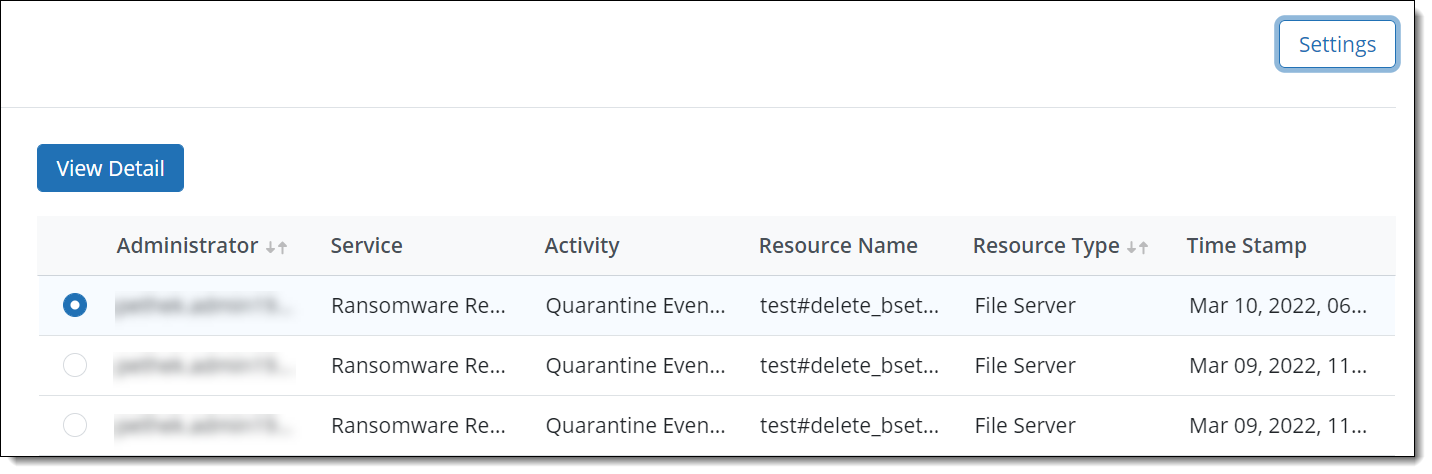
The Audit Trails page provides a quick view of the actions performed by various administrators.
If you are interested in seeing detailed information such as the summary why did the admin take the action and other additional information, use this feature to view the details.
Select the Audit Trail and then click on View Detail.
Filter Audit Trails
There is a wide array of filters to view details of the administrator activities on Ransomware Recovery Management Console. The filters can be applied concurrently along with the Time Period filter to fetch the Audit Trail Report.
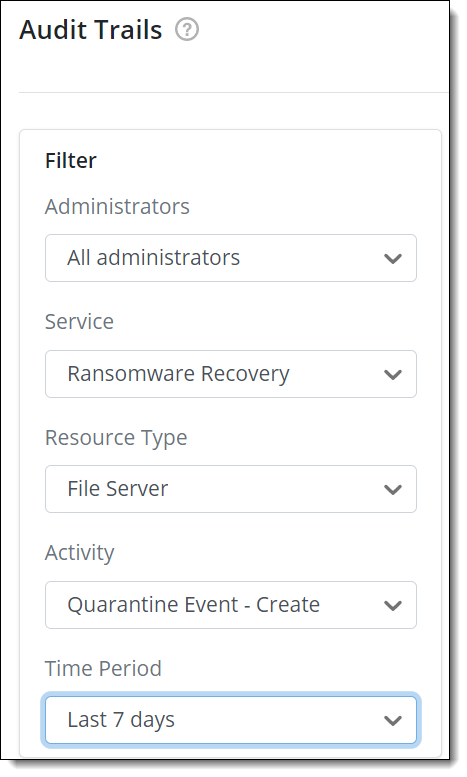
The following table lists the Audit Trail filters.
| Filter | Description |
|
Administrators |
The administrator who performed the activity. You can select All Administrators or the specific administrator who performed the activity. By default, the Administrator list displays the All Administrators value. |
| Service | The name of the Druva Service in which the activity was performed. Example - Ransomware Recovery |
|
Resource Type |
The type of Ransomware Recovery resources. The resource list includes Endpoints, OneDrive, Google Drive, SharePoint, Shared Drive, File hash, Windows/Linux File Servers, NAS, and so on. By default, the Resource Type list displays the All Resources value. |
|
Activity |
The activity or action performed by the administrator. The values of this filter appear based on the resource and entity types you select. For example, if you select Ransomware Recovery > Endpoint in the Resource Type list, the Action list displays action values corresponding to the selection, such as Malicious File Scan - Job Created. By default, the Action list displays the All Actions value. |
|
Time Period |
The timeframe to track audit trail. The values include Last 24 hours, Last 7 days, Last 30 days, Last 3 months, Last 6 months, Last 1 year. Select the appropriate time period from the list to specify the duration in which the activities were performed. The time period values that appear in this filter is based on the configured Audit Trails Retention Policy. For more information, see Manage Audit Trails. |
Related Links

